Small businesses are no longer invisible to cybercriminals. Today, automated attacks, ransomware-as-a-service, and mass phishing campaigns actively target small and medium-sized companies because they often lack mature security processes. Cybersecurity for small businesses is no longer optional – it is a critical part of operational stability, data protection, and customer trust.
For startups and SMBs, a single breach can result in financial losses, downtime, regulatory penalties, and long-term reputational damage. This guide explains how to build effective small business network security, protect data, and reduce cyber risks using practical, scalable approaches.
Why Cybersecurity Matters for Small Businesses
.png)
Cybersecurity directly affects business continuity. Small businesses increasingly rely on cloud infrastructure, digital communication, online payments, and remote access – all of which expand the attack surface.
Key reasons cybersecurity matters for small businesses include:
- Financial impact: Ransomware and fraud attacks often demand payments that exceed a small company’s cash reserves.
- Operational disruption: Downtime caused by malware or network compromise can halt sales, logistics, or customer support.
- Data protection obligations: Customer and employee data must be protected to comply with privacy and industry regulations.
- Trust and reputation: Clients expect businesses to safeguard sensitive information, regardless of company size.
A proactive cybersecurity strategy reduces risks before incidents occur, rather than reacting after damage is done.
Biggest Cyber Threats Facing Small Businesses Today
Understanding threats is the foundation of effective cybersecurity for small businesses. Most attacks rely on common weaknesses rather than advanced techniques.
Malware and Ransomware
Malware infections often enter networks through malicious downloads or infected email attachments. Ransomware encrypts business data and demands payment for recovery, frequently targeting businesses without reliable backups.
Phishing and Social Engineering
Phishing remains the most common entry point for attackers. Emails or messages impersonate trusted contacts to steal credentials, deploy malware, or gain network access.
Weak Authentication and Passwords
Poor password hygiene, password reuse, and lack of multi-factor authentication make it easy for attackers to compromise accounts.
Unpatched Vulnerabilities
Outdated systems, missing updates, and unsupported software expose known vulnerabilities that attackers actively exploit.
Insecure Cloud and Remote Access
Misconfigured cloud services, unsecured VPNs, and unmanaged endpoints increase the risk of unauthorized access to business infrastructure.
Small Business Network Security Basics
Small business network security focuses on protecting internal systems, internet connections, and connected devices from unauthorized access and threats.
Core elements of business network security include:
- Firewalls to control inbound and outbound traffic
- Secure network segmentation to isolate critical systems
- Endpoint protection for devices such as laptops and mobile phones
- Monitoring and logging to detect suspicious activity
- Access control based on user roles and responsibilities
Network security for business environments must balance protection with usability, ensuring employees can work securely without unnecessary complexity.
How to Secure a Business Network
Securing a business network requires a layered and systematic approach. For small businesses, network security is not about deploying complex enterprise-grade solutions, but about building reliable protection across infrastructure, access points, and connected devices.
Implement Firewalls and Network Perimeter Protection
A firewall is the foundation of business network security. It controls incoming and outgoing traffic, blocks malicious connections, and limits exposure to external threats. Small businesses should use business-grade firewalls that support traffic filtering, intrusion prevention, and logging. Proper firewall configuration helps prevent unauthorized access and reduces the risk of malware spreading inside the network.
Secure Routers, Wi-Fi, and Internet Access
Network security for small business environments starts with secure internet access. Default router settings must be changed immediately, including administrator credentials. Wireless networks should use strong encryption and separate guest access from internal systems. This prevents external users or compromised devices from reaching sensitive business resources.
Apply Network Segmentation
Network segmentation is a critical but often overlooked security practice. By separating workstations, servers, cloud services, and critical systems into different network zones, businesses limit the impact of potential breaches. If one segment is compromised, attackers cannot easily move across the entire network.
Control Access and Authentication
Access management plays a central role in securing a business network. Employees should only have access to systems required for their role. Strong passwords, multi-factor authentication, and regular access reviews significantly reduce the risk of unauthorized entry caused by compromised credentials.
Monitor Network Activity and Endpoints
Continuous monitoring allows businesses to detect unusual behavior early. Network monitoring tools help identify suspicious traffic, failed login attempts, or unexpected data transfers. Endpoint protection on laptops, desktops, and mobile devices adds another layer of defense, especially for remote or hybrid teams.
A secure business network is built through consistent controls, regular updates, and ongoing monitoring. When combined, these measures create a resilient security foundation that protects operations, data, and customer trust.
Small Business Network Security Checklist
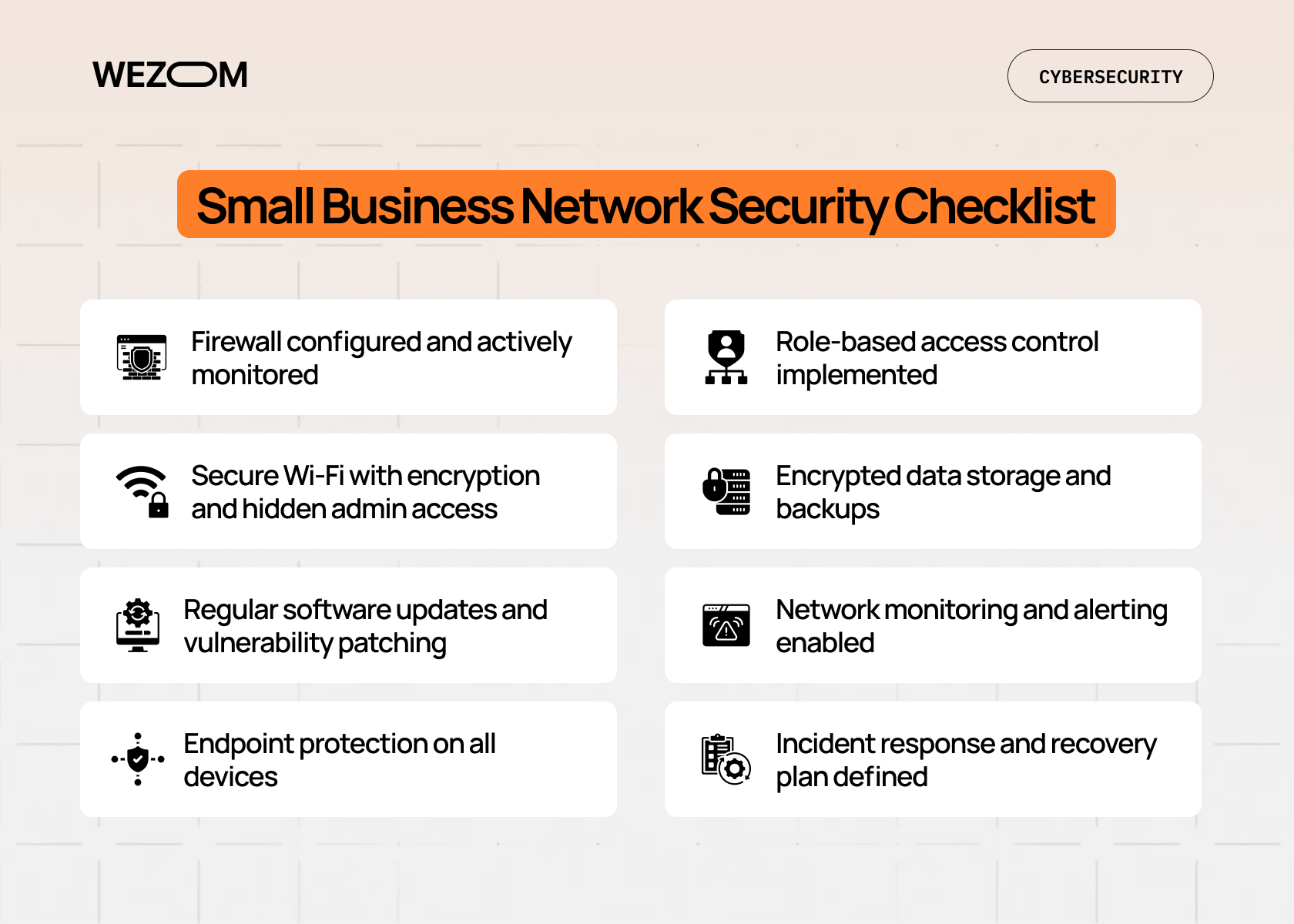
A practical small business network security checklist helps ensure that essential controls are in place:
- Firewall configured and actively monitored
- Secure Wi-Fi with encryption and hidden admin access
- Regular software updates and vulnerability patching
- Endpoint protection on all devices
- Role-based access control implemented
- Encrypted data storage and backups
- Network monitoring and alerting enabled
- Incident response and recovery plan defined
This checklist supports both network security for small business environments and broader cybersecurity goals.
Data Protection for Small Businesses
Data protection for small businesses focuses on preventing unauthorized access, loss, or exposure of sensitive information.
Encryption and Secure Storage
Encryption protects data both at rest and in transit, ensuring that stolen information cannot be easily exploited.
Backup and Recovery
Reliable backups are essential protection against ransomware and system failures. Backups should be:
- Automated and frequent
- Stored securely offsite or in the cloud
- Regularly tested for successful recovery
Privacy and Compliance
Depending on industry and location, businesses may be subject to data protection regulations. Clear policies for data access, retention, and deletion reduce compliance risks.
Cybersecurity Tools for Startups and SMBs
Cybersecurity tools for startups should be scalable, easy to manage, and cost-effective.
Common categories of cybersecurity tools for SMBs include:
- Firewall and network security solutions for traffic control
- Endpoint protection platforms to detect malware and threats
- Email security tools to prevent phishing and spam
- Backup and recovery solutions for business continuity
- Monitoring and vulnerability management tools for ongoing protection
At WEZOM, cybersecurity services for SMBs are designed to integrate network security solutions for small businesses with existing infrastructure, focusing on risk reduction rather than unnecessary complexity.
Best Practices for Network Security
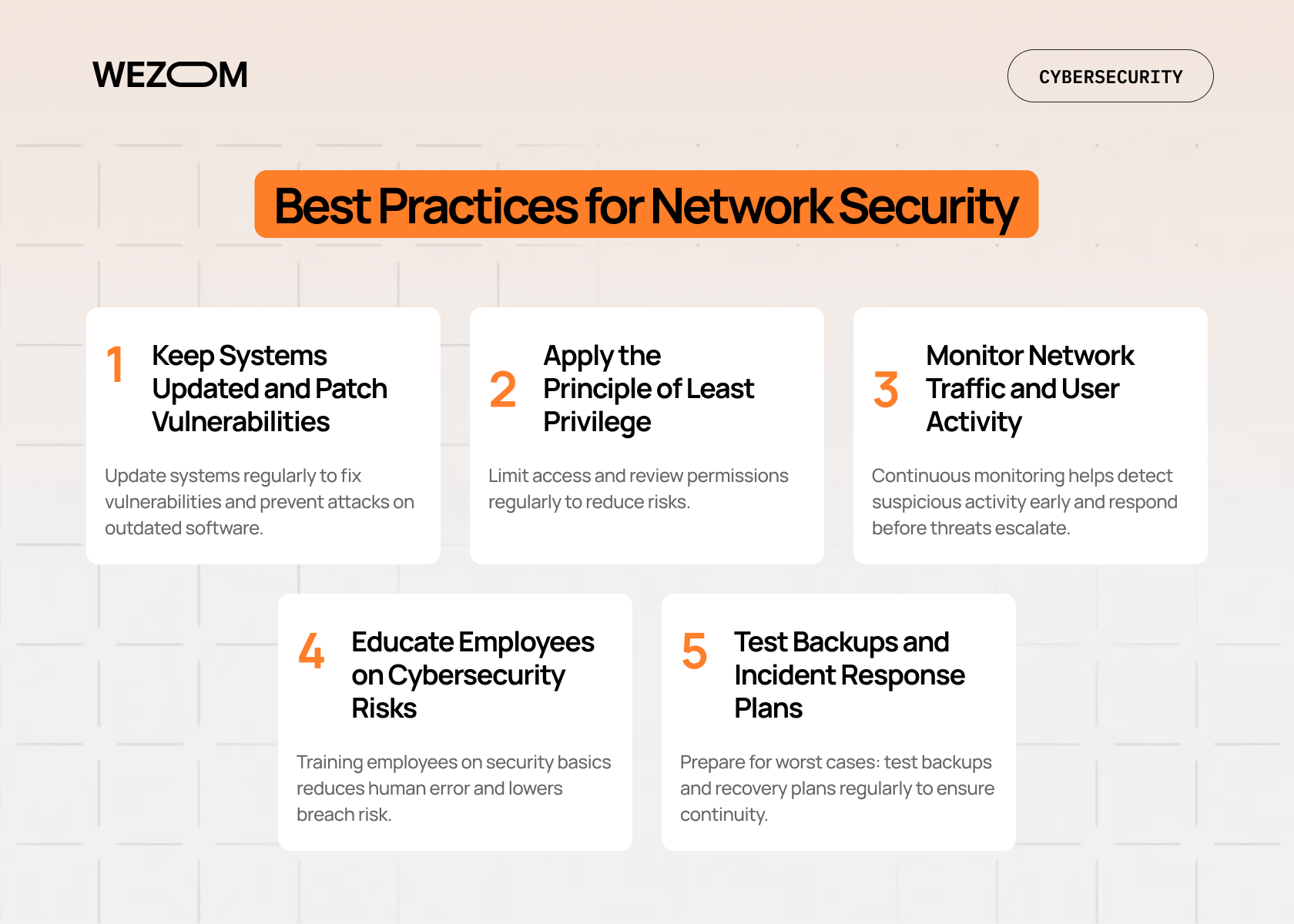
Network security best practices help small businesses maintain consistent protection as infrastructure, teams, and digital tools evolve. Unlike one-time security setups, best practices focus on ongoing risk reduction and operational resilience.
Keep Systems Updated and Patch Vulnerabilities
Regular software updates are one of the most effective security measures. Operating systems, routers, firewalls, and applications must be updated to eliminate known vulnerabilities. Attackers often exploit outdated systems rather than advanced technical flaws.
Apply the Principle of Least Privilege
Access rights should be limited to what employees need to perform their tasks. Reducing unnecessary access lowers the risk of internal misuse and limits the damage if an account is compromised. Access permissions should be reviewed regularly, especially when roles change.
Monitor Network Traffic and User Activity
Continuous monitoring enables early detection of suspicious behavior, such as abnormal data transfers or repeated authentication failures. Network monitoring tools help small businesses respond to threats before they escalate into major incidents.
Educate Employees on Cybersecurity Risks
Human error remains a leading cause of security breaches. Regular training on phishing, password hygiene, and safe device usage significantly reduces risk. Employees should understand how their actions affect overall network security.
Test Backups and Incident Response Plans
Best practices for network security include preparation for worst-case scenarios. Backup systems and recovery plans should be tested regularly to ensure business continuity after ransomware attacks, system failures, or data loss incidents.
Consistently applying these best practices strengthens small business network security and creates a proactive security culture rather than a reactive one.
Common Cybersecurity Mistakes Small Businesses Make
Despite good intentions, many small businesses repeat avoidable mistakes:
- Relying solely on antivirus software.
- Ignoring updates and security patches.
- Using shared or weak passwords.
- Lack of employee training on phishing risks.
- No tested backup or recovery plan.
Addressing these issues significantly improves overall cybersecurity posture without major investment.
Building effective cybersecurity for small businesses is a continuous process. With the right network security solutions for small businesses, clear policies, and practical tools, startups and SMBs can protect their infrastructure, data, and long-term growth.

FAQ
What is network security for small businesses?
Network security for small businesses refers to the processes, tools, and controls used to protect business networks from unauthorized access, malware, and data breaches. It includes firewalls, access control, monitoring, and secure network configurations.
How can a small business secure its network?
A small business can secure its network by using firewalls, enforcing strong authentication, segmenting network access, keeping systems updated, and continuously monitoring for threats. Following a small business network security checklist helps ensure consistent protection.
What are the most common cybersecurity threats for SMBs?
The most common threats include phishing, ransomware, malware infections, weak passwords, and unpatched vulnerabilities. These threats often target small businesses due to limited security resources.
What is the best way to protect business data?
The best approach combines encryption, regular backups, access control, and employee awareness. Data protection for small businesses should focus on both prevention and recovery.
What should a business do after a cyberattack?
After a cyberattack, a business should isolate affected systems, assess damage, restore data from backups, investigate the cause, and update security controls to prevent recurrence. Having a predefined incident response plan reduces recovery time and impact.

