Any digital solution launched into the public domain must function legally, right? And when it comes to legality, the first thing that comes to mind is usually ensuring compliance with the GDPR.
However, along with the well-known GDPR, which contains provisions on the protection of confidential user data and has been valid for EU residents since 2018, the US governance adopted its analog for California residents, CCPA, at the beginning of 2020. Below, we will tell you in more detail how to achieve compliance with this law.
What Are the CCPA Requirements?
In a nutshell, the California Consumer Privacy Act (CCPA) defines the appropriate level of control that consumers have over their data and how it is processed by organizations that use it.
The main provisions of this act are:
- Right to Know, which ensures that organizations provide their consumers with all the necessary information about how their personal data is collected, stored, used, and shared;
- Right to Delete, which determines the ability to delete the personal data of those consumers who have left a corresponding request to the organization;
- Right to Opt-Out, which gives consumers the right to choose whether to sell or share their personal data;
- Right to Limit Use and Disclosure of Sensitive Personal Information, which allows consumers to limit access to their sensitive personal data;
- Private Right of Action, which determines the ability of consumers to file claims against organizations that do not sufficiently reliably protect their data;
- Privacy Policy Disclosures, which imposes on organizations the responsibility to notify users about the collection of their personal data for processing and sharing.
All of these rights apply to absolutely all data types that have been collected by organizations from their consumers, including financial, contact, medical, and so on. They must also act in accordance with the consumers’ needs to delete, prohibit the sale, control, and transfer of their personal data.
Finally, note that the CCPA also provides for the introduction of a data privacy regulation (CDR) tax, which supports the functioning of administrative bodies responsible for monitoring compliance with the law.
What's the Difference Between CCPA vs. GDPR?
While the CCPA and GDPR are similar in many ways, they are not the same.
| Aspect | GDPR | CCPA |
| Scope of Data | Any personal data | Exclusively consumer data |
| Definition of Personal Data | Broad: Any information related to an identified or identifiable person | Specific: Data directly provided by a consumer |
| Geographical Scope | Applies to organizations within the EU and those dealing with EU residents' data globally | Applies to businesses in California or dealing with California residents |
| Individual Rights | Various rights including access, rectification, erasure, restriction of processing, data portability, and objection | Rights include knowing what personal data is collected, opting out of data sale, and requesting deletion of personal data |
| Compliance Mechanism | Comprehensive measures including Data Protection Officers (DPO), Data Protection Impact Assessments (DPIA), and strict consent requirements | Less prescriptive, focuses on providing clear opt-out options and transparent notices |
| Penalties for Non-Compliance | Up to 4% of annual global turnover or 20 million euros, whichever is higher | Up to $7,500 per violation |
| Consent Requirements | Requires explicit consent for data processing, with clear opt-out mechanisms | Allows businesses to collect data without explicit consent but requires them to provide an opt-out option for data sale |
| Data Breach Notifications | Must notify data subjects within 72 hours of becoming aware of a breach | Must notify consumers if unencrypted and unredacted personal information is exposed |
In reality, there are many more differences, and we are confident that over time, as GDPR and CCPA are expanded with new provisions, their list will become even longer.
What Are CCPA Penalties for Violating Compliance Requirements?
Above, we have already outlined the approximate amount of the fine that is imposed on organizations that violate the CCPA – it is up to $ 7,500 for each identified case. At the same time, given the relative "youth" of this law, it is difficult to talk about how much the risk is that you will face fines.
That is why we suggest that you consider specific cases when the violation of user rights (not only CCPA) to control their personal data caused losses for many world-famous organizations:
- Google, which was fined 17 million dollars for failing to provide users with adequate information about how exactly their location data is collected and used;
- Facebook, which in 2019 was fined 5 billion dollars for violating the privacy of consumer data related to the Cambridge Analytica scandal;
- Equifax, which in 2017 compensated its customers $700 million for failing to take timely measures to protect user data from cyberattacks (in particular, due to one of them, the personal information of more than 147 million people was stolen);
- Uber, which in 2020 had to pay $8 million for the arbitrary disposal of user location data;
- TikTok, which in 2020 was fined $27 million for illegally collecting personal data of children without obtaining prior consent from their parents;
- Robinhood, which paid $1.65 million in 2020 for failing to provide consumers with information about how their orders would be routed, resulting in conflicts of interest and harm to the customers;
- Sephora, which was fined $1.2 million in 2021 for failing to clearly communicate what protection measures were applied to their personal data;
- DoorDash, which was obligated to pay the $2.5 million penalty in 2022 for failing to properly secure user data, resulting in a data breach;
- Aeromexico, which was fined $1 million in 2023 for delays in processing consumer requests to restrict the use of their personal information;
- RealReal, which was fined $2 million in 2023 for using and selling its consumers' personal data without their consent.
Of course, smaller companies usually face smaller fines, but that doesn't mean you should neglect the CCPA security controls when you distribute your software in the state of California in particular.
Step-by-Step Guide to CCPA Compliance
Now, let's learn how to ensure CCPA data compliance step by step.
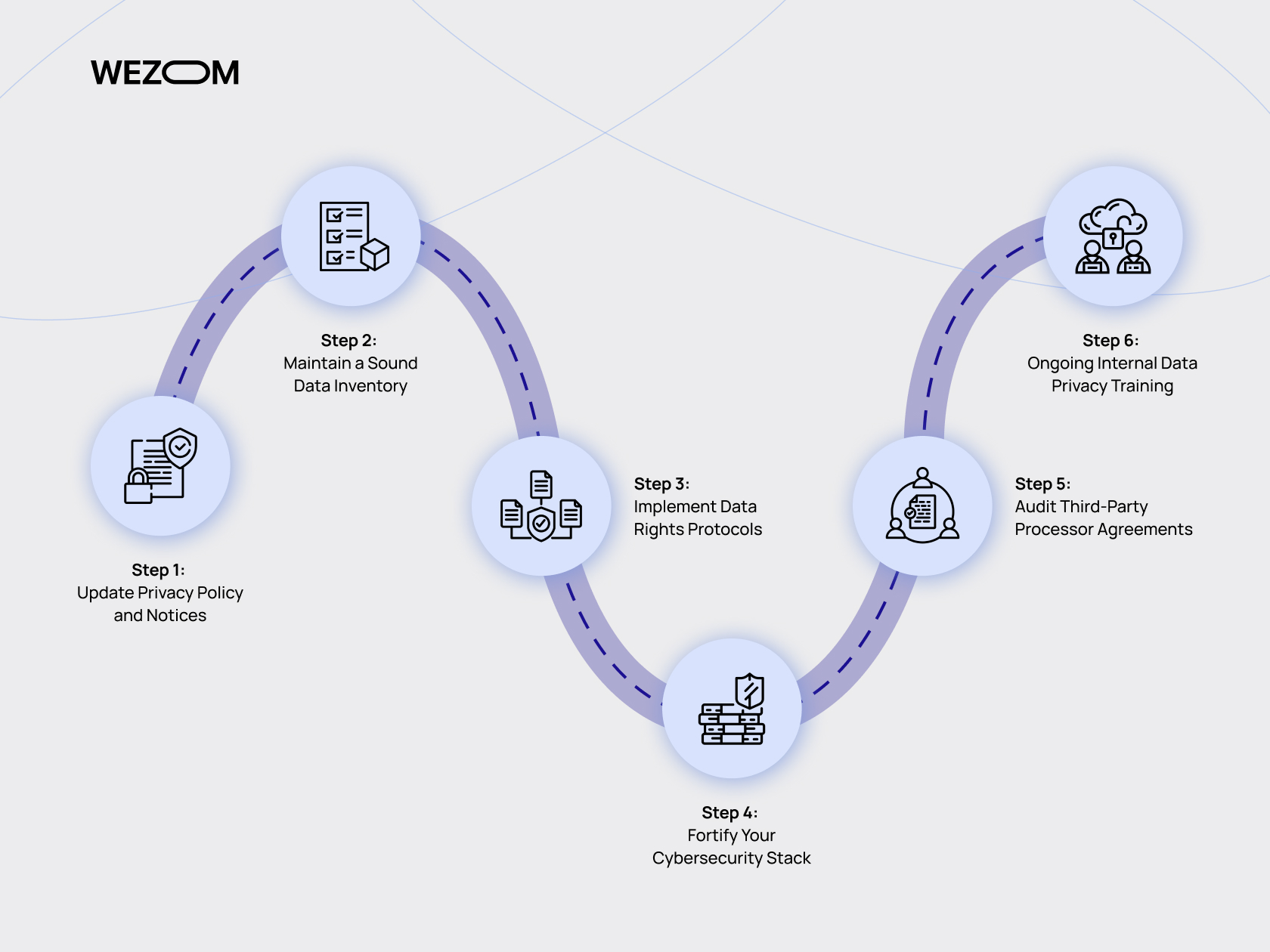
Step 1: Update Privacy Policy and Notices
Start by updating your existing consumer data privacy policies to define what their data means in the context of the CCPA. Address any gaps, particularly by ensuring that your consumers are well-informed about how you will collect, use, and share that data.
Step 2: Maintain a Sound Data Inventory
Perform a comprehensive data inventory that, in addition to the consumer data itself, will take into account what actions are performed with it. Also, make sure that this monitoring checks the software and equipment used – they must also meet the CCPA data requirements. Finally, pay special attention to processes that involve the transfer of consumer data to third parties – each of them also must comply with the norms of this act.
Step 3: Implement Data Rights Protocols
Optimize processes that interfere with consumers' unimpeded access and control over their data. You will likely need to implement entire protocols that will tell your employees how and what to do in the event of a specific consumer request, in order to minimize the time it takes to complete it.
Step 4: Fortify Your Cybersecurity Stack
Conduct global research on what methods and approaches you currently use to protect consumer data. Specifically, to meet CCPA compliance requirements, you may need to update some data transfer protocols, apply AES data encryption, or replace anything else that does not provide the necessary level of security.

Step 5: Audit Third-Party Processor Agreements
If your organization collaborates with other companies and shares consumer data in those collaborations, you will need to prepare and implement agreements that will govern the security of that data when it is shared with those companies. You will also need to notify your consumers of the potential for such sharing.
Step 6: Ongoing Internal Data Privacy Training
Finally, to complete your CCPA compliance protection measures, you will need to train your employees on the rules and policies that will ensure that consumer information is not leaked due to their fault. Consider what training methods will bring the most benefit to your organization without taking up too many resources – both yours and your employees (for instance, you should consider online training).
You will also need to conduct testing at the end of the CCPA data security requirements training to ensure that all the necessary knowledge has been successfully obtained.
How Does Wezom Help with the CCPA?
To summarize the above, we can say that ensuring compliance with CCPA guidelines for products and services that are permitted for use by California residents is not only a guarantee of the absence of possible fines (in particular, those related to the violation of consumer privacy or abuse of their private data use) but also strengthening their competitive advantage in the market. Indeed, your audience will have greater loyalty to your digital solution if they know that it fully complies with the laws that apply in their territory of residence.
If you are looking for a team that will create software for you in full compliance with all the CCPA data security policies, feel free to contact us. We have been creating cutting-edge, CCPA compliant solutions since the very beginning of the adoption of this act – that’s why we are confident that we will cope perfectly with your task, no matter how complex and non-trivial it may be.
